Difference between revisions of "UTA Security Matrix"
| Line 9: | Line 9: | ||
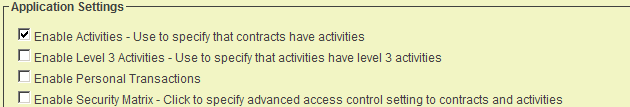
1. Click the '''Settings''' tab. | 1. Click the '''Settings''' tab. | ||
| − | 2. Click the | + | 2. Click the [[UTA Settings - Security|Security tab]]. |
| − | The '''Security Matrix''' setting is displayed in the ''' | + | The '''Security Matrix''' setting is displayed in the '''Security Settings'''. |
[[Image:Uta135.png]] | [[Image:Uta135.png]] | ||
| Line 19: | Line 19: | ||
4. Click the '''Save''' button. | 4. Click the '''Save''' button. | ||
| − | The '''Security Matrix''' link is added to the top of the ''' | + | The '''Security Matrix''' link is added to the top of the ''''Security Settings''' window. |
[[Image:Uta136.png]] | [[Image:Uta136.png]] | ||
Revision as of 14:38, 22 July 2013
Contents
Enabling the Security Matrix
Once you have created your Universal Tracking Application you may want to restrict interaction with the application and the associated entities. In order to do this you will need to enable the Security Matrix feature.
You should only enable this feature when you have completed the entire application, as it may become very difficult to work with the application once this security is switched on.
The Security Matrix is configured from the Configuration page.
1. Click the Settings tab.
2. Click the Security tab.
The Security Matrix setting is displayed in the Security Settings.
3. Click the Enable Security Matrix check box.
4. Click the Save button.
The Security Matrix link is added to the top of the 'Security Settings window.
As soon as the security matrix is enabled, all users will lose all access to data within the application until the permissions are established.
5. Click the Security Matrix link.
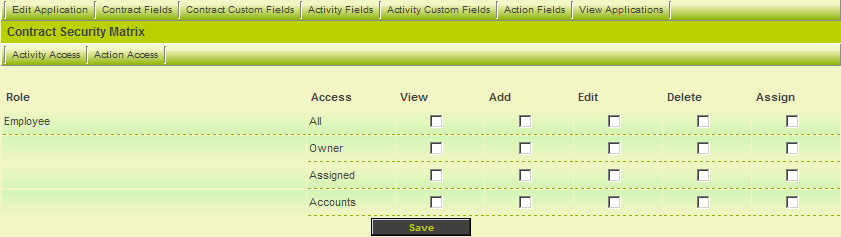
The Security Matrix window is displayed.
How the Security Matrix works
- The current view is for security associated with the Contract level.
- Two additional tabs are used to control security associated with the Activity and Action levels.
For each role that you have permissioned to access the application, the same set of options will be displayed at each level.
Role Engagement
All access is role based. Each set of access permissions can be set based on the following role engagement:
- All – All users in this role can perform the permissioned actions.
- Owner – Only a user in this role associated through the “Owner” standard field can perform the permissioned actions.
- Assigned – Only users in this role that are assigned to the item perform the permissioned actions.
- Accounts – Only users in this role that are associated with organisations assigned to this item perform the permissioned actions. This is an indirect permission. For example, if you were to associate a company with a project and use this permission, then someone from that company with this role would be able to perform the permissioned actions.
Permission Types
The following five permission types are available:
- View – View the item.
- Add – Create a new item.
- Edit – Edit an existing item.
- Delete – Delete an existing item.
- Assign – Assign other contacts to the item.
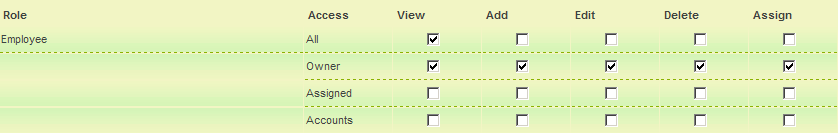
Setting the Security Matrix
1. Set the permissions as shown below:
- All employees can view all items.
- Only the owner can view, add, edit, delete and assign other people.
2. Click the Save button.
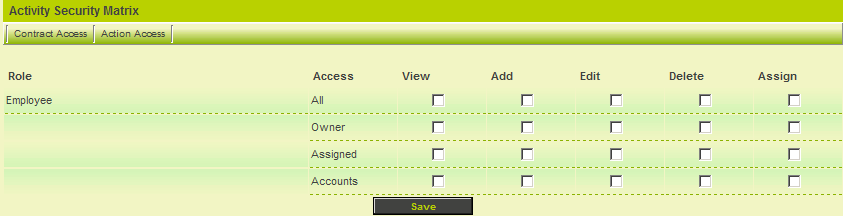
3. Click the Activity Access tab.
The same set of roles and permissions are displayed, but this time for the Level 2 items.
4. Set the permissions the same as for the Level 1 items.
5. Click the Save button.
6. Repeat this process for Level 3 – Actions.