Multi-Factor Authentication
Contents
When using two-factor authentication, each new user can use Google Authenticator to obtain one-time passwords, calculated from algorithms which are time and/or event-based.
Definition of "Two-Factor Authentication"
Most websites where one can login require a username and password. While a username and a password are two different things they are both "known" by the individual logging in. In short, this means that anyone who knows the username and password can login, thus there is very little that can be done to identify that the individual logging in is actually the individual who owns the account.
Enter factor two. The second factor can be something that someone has or some unique property of that person. The former could refer to an access card and the latter would refer to a fingerprint.
As you can see, one may lose an access card or get duped into sharing a password, but the odds of both happening are greatly reduced. Using Two-Factor Authentication enhances an organization's ability to ensure that no one is using illegitimate means to gain access.
Configuring a Role to Use Two-Factor Authentication
- Two-Factor Authentication is configured by User Role.
- For roles that have this feature enabled, the use of Two-Factor Authentication becomes mandatory.
- Click on Roles & Permissions (located on the Configuration Menu on the left-hand navigation bar)
- Click on the hyperlink for User Roles
- Click the Edit button next to the role for which you wish to add Two-Factor Authentication
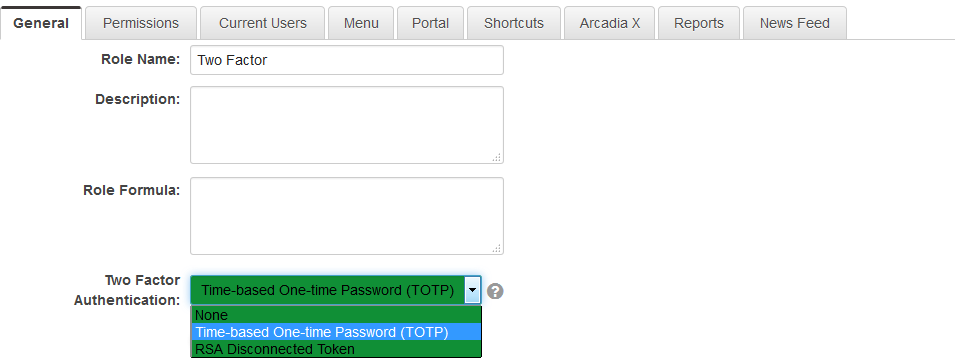
- Click on the drop-down for the Two-Factor Authentication option. There are a number of options exposed:
- None
- Time-based One-time Password (TOTP)
- RSA Disconnected Token
- Hit Save.
- Use Send Password button on user profile to send them an email with Activation link.
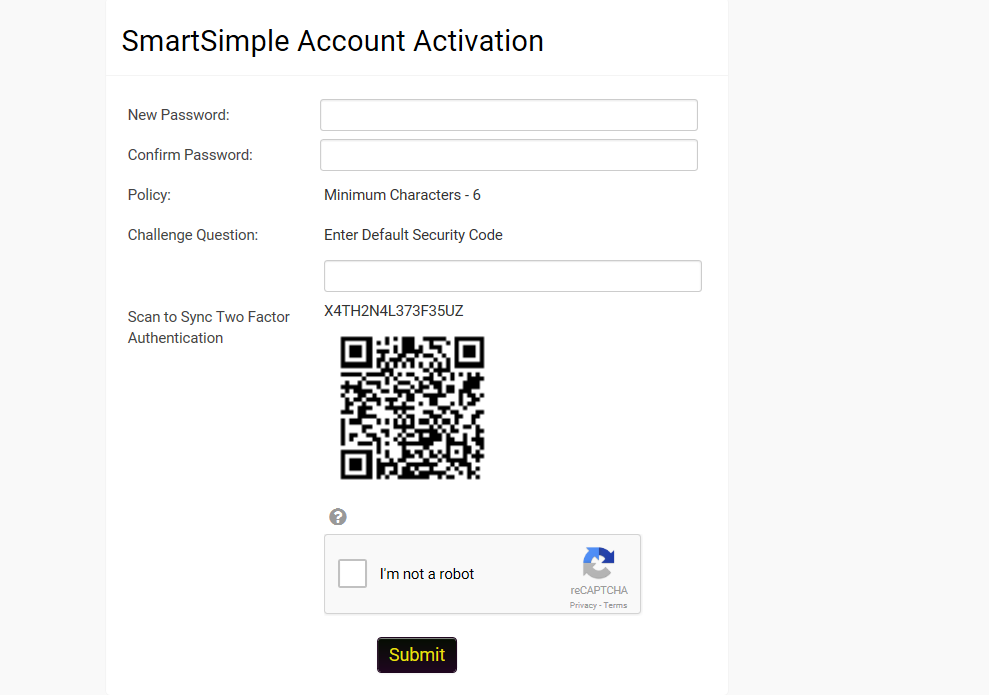
When the user receives the new password then they navigate to the activation screen.
If this is the first time the user has had a code generated then the screen should include a QR Code that can be scanned using Google Authenticator. The actual authentication code is also provided in case there are issues with the use of Google Authenticator.
If the user has an existing QA Code then the user can click a button to generate a new code and re-sync or can proceed to the login page.
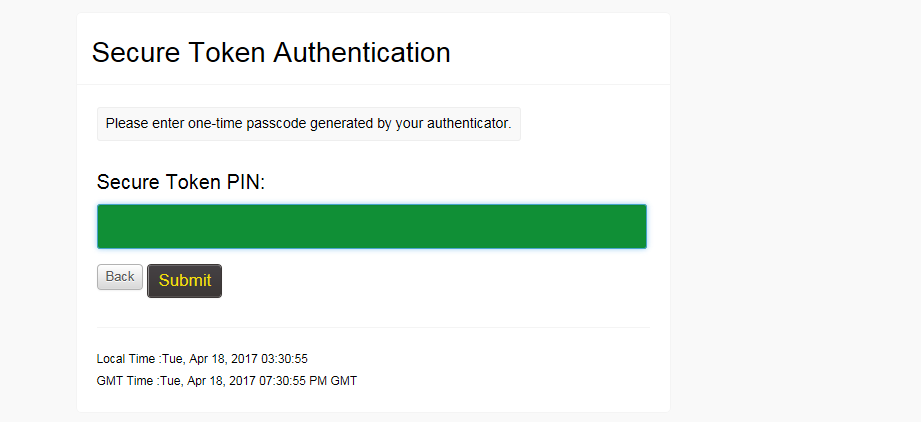
Users will then be prompted to enter the one-time code after entering their user name and password.
Notes
- If both Single Sign-On and Two-Factor Authentication are in use, there is a Single Sign-On setting option that will control whether or not Two-Factor Authentication will be required when a user authenticates via SSO.