Multi-Factor Authentication
Contents
Overview
Multi-Factor Authentication is a method of authentication in which a user is granted access to your SmartSimple Cloud system only after successfully presenting two or more pieces of evidence to an authentication mechanism.
The security impact of Multi-Factor Authentication (MFA) is that while a user may lose an access card or get tricked into sharing a password, the odds of both happening to a single user are dramatically reduced. Using MFA therefore enhances an organization's ability to ensure that no one is using illegitimate means to gain access.
SmartSimple Cloud supports two different approaches to Multi-Factor Authentication:
- Time-based One-Time Password (TOTP) via an authenticator app.
- IMPORTANT: YOU MUST setup your authenticator app and link to your user account BEFORE enabling this type of MFA if you are an existing user. Additional steps are required. Please see below for details.
- Single Use Verification Code sent by either Email or SMS.
- No additional configuration steps required for this type of MFA.
Configuration - Essentials
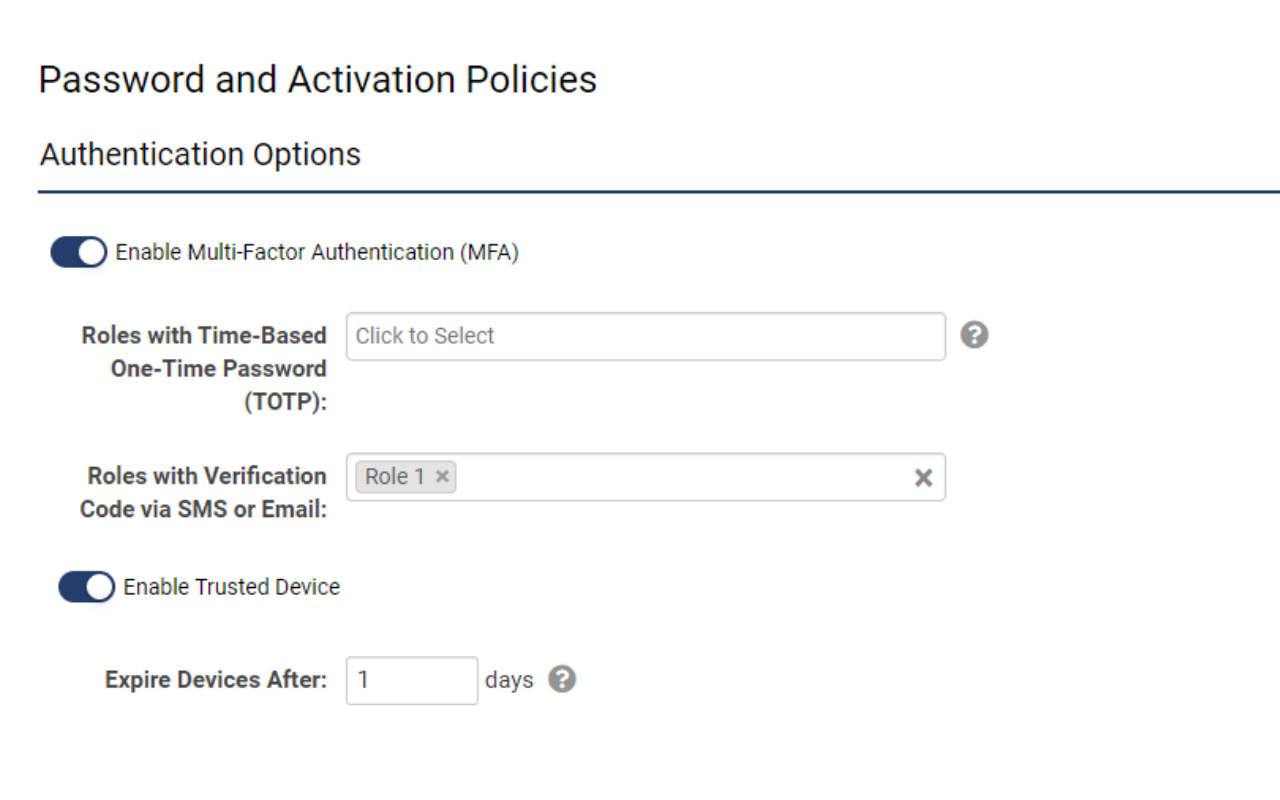
All settings related to multi-factor authentication are in a single location
- Navigate to Global Settings > Security > Password and Activation Policies
- Scroll to Authentication Options and toggle on Enable Multi-Factor Authentication
- Specify the roles that require authentication via TOTP and/or Verification Code
NOTE: If new roles are added to the system, the MFA configuration must also be updated
Setting up Verification Codes for Email
The easiest way to set up MFA is through the email that was used for user registration and login. Be sure to follow the instructions carefully to avoid accidentally locking yourself or others out of their accounts.
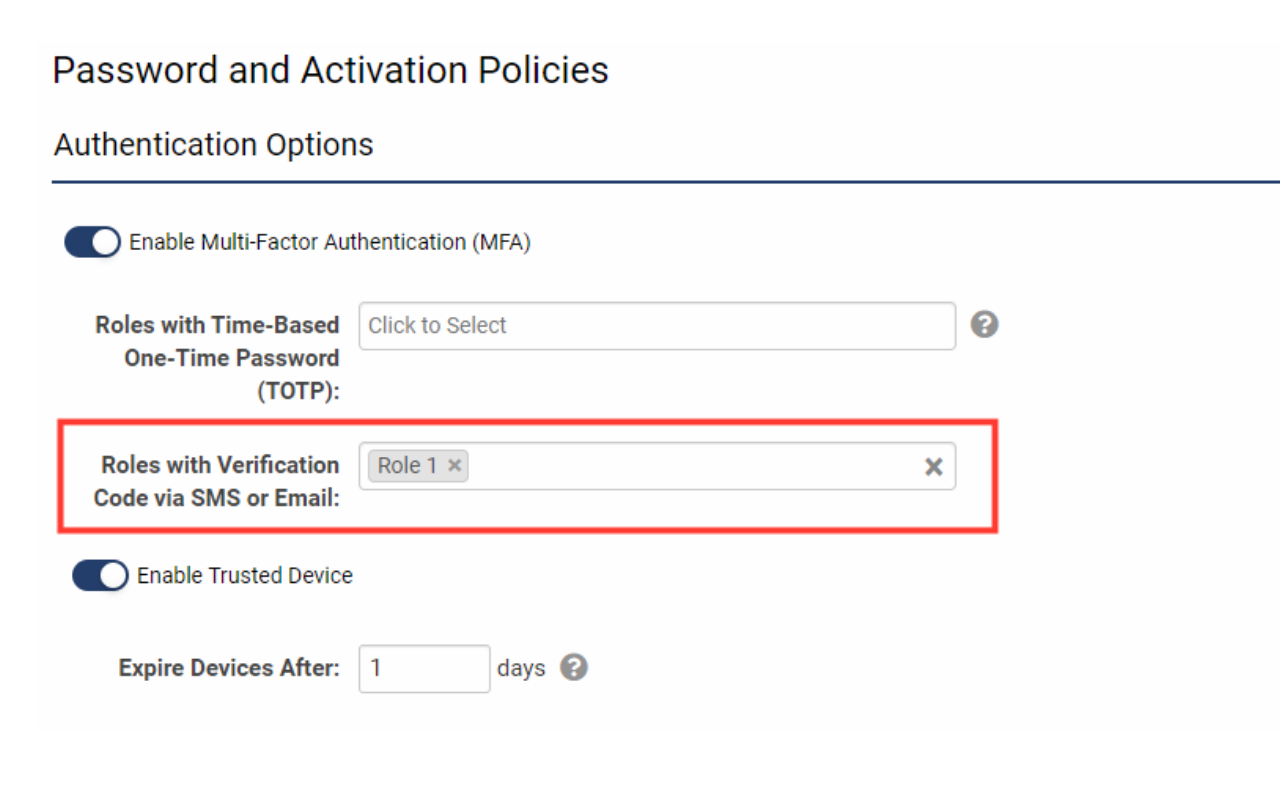
- Go to Menu Icon > Global Settings > Security tab > Password and Activation Policies and then scroll down to the section marked Authentication Options.
- Toggle on Enable Multi-Factor Authentication. You will see additional settings displayed for different authentication methods.
- Under the Roles with Verification Code via SMS or Email setting, you will need to decide which roles need to be authenticated via a verification code sent through the email address used for login. Ensure that users assigned to this role have not opted out of receiving system emails. Click the Save button at the bottom of the page to activate changes.
Logging in with a Verification Code from Email
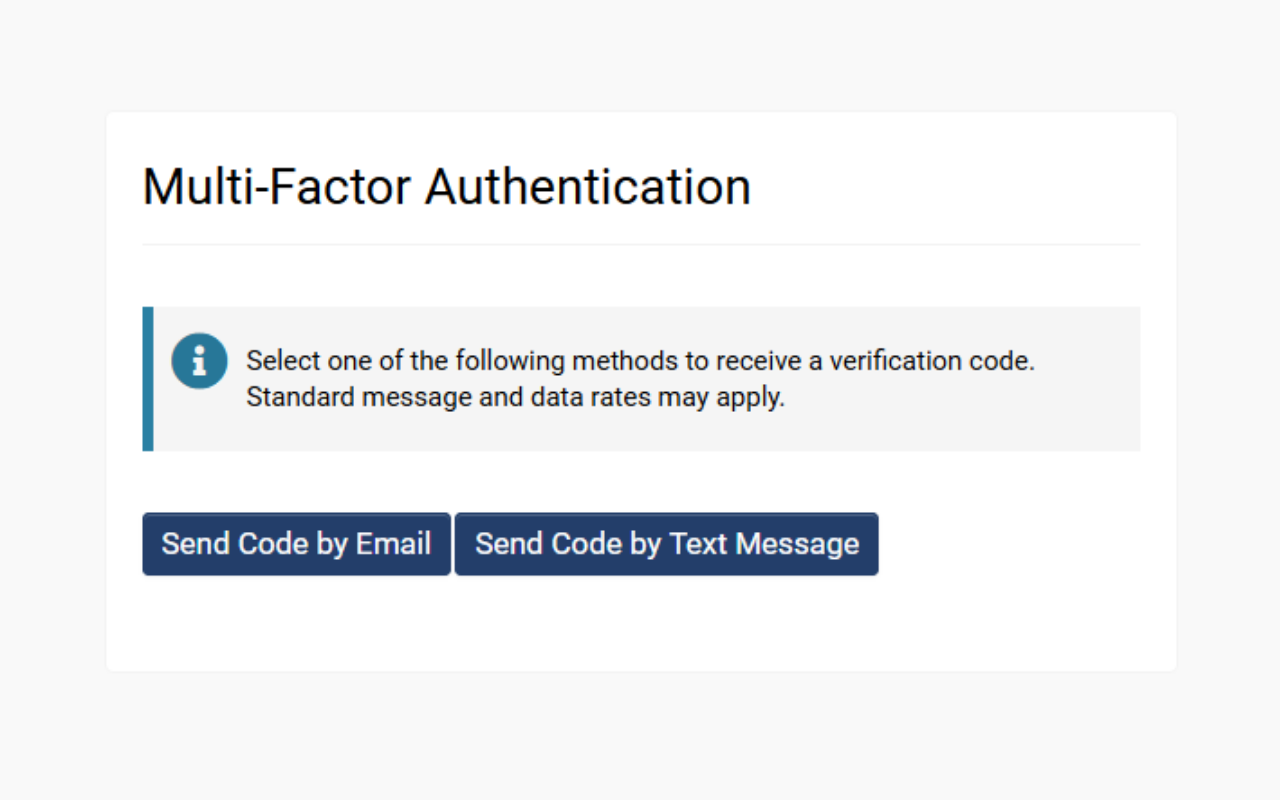
When a user has been assigned a role that requires a verification code, they can login using the following steps:
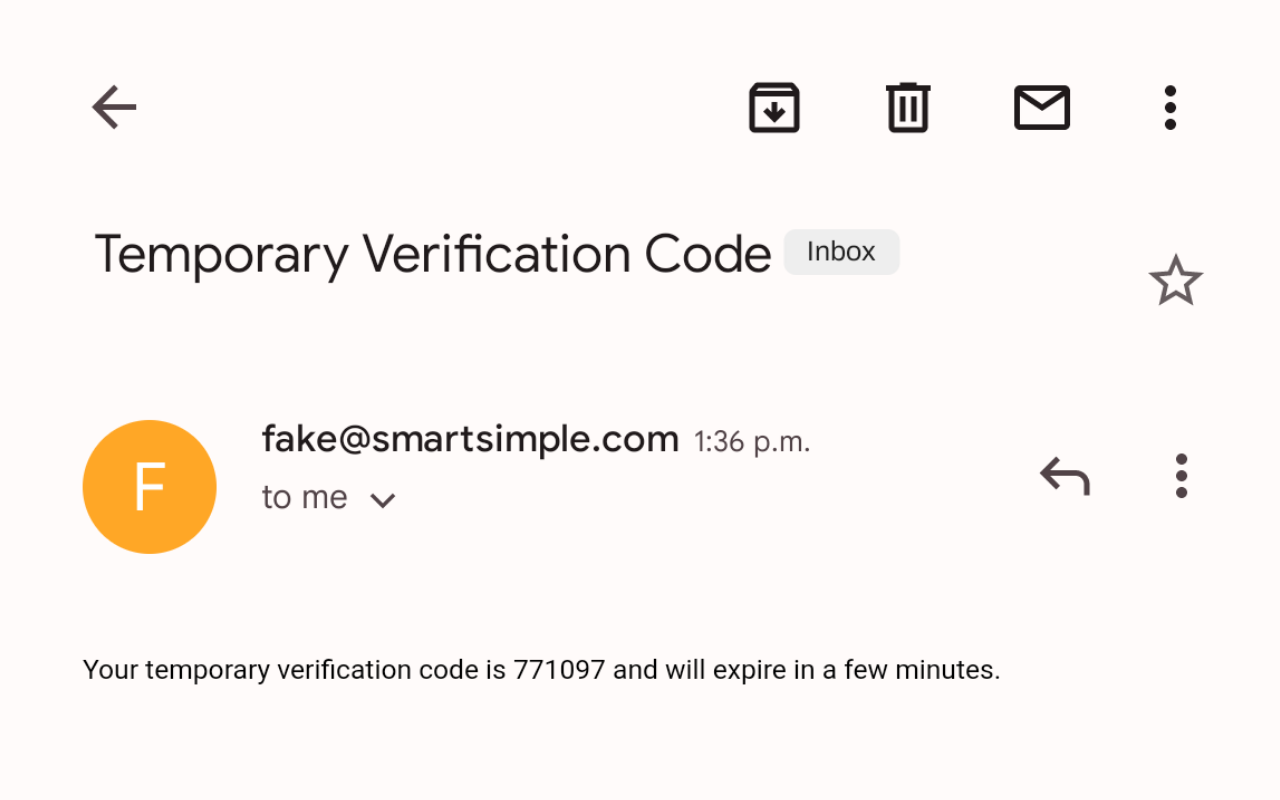
- When the user logs in using their email and password, they will be prompted to enter a verification code that was sent to their email.
- The user can check their email to copy the verification number.
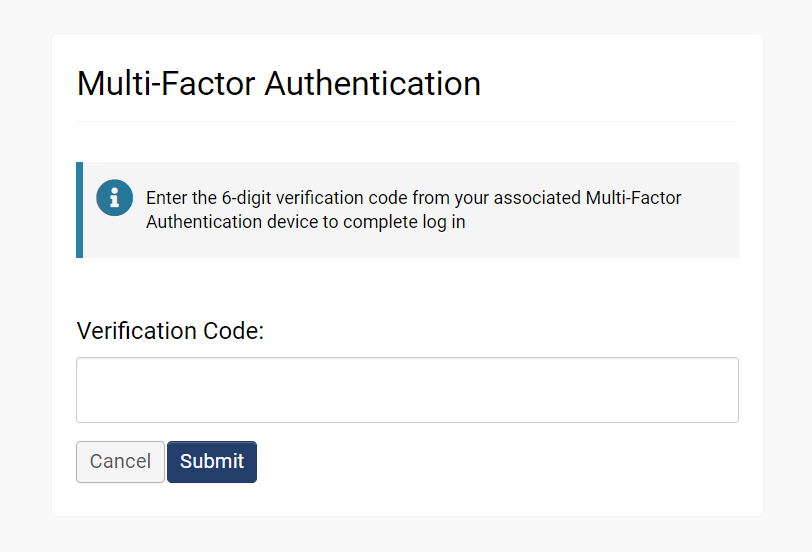
- Enter the verification code into the field and then click Submit to finish authenticated login.
Setting up Verification Codes for SMS
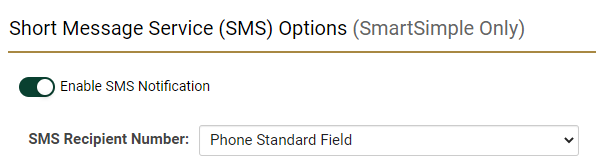
In order for users to receive SMS messages, a SmartSimple administrator must first enable SMS services by going to Menu Icon > Global Settings > Communications tab > Toggle on Enable SMS Notification.
Logging in with a Verification Codes for SMS
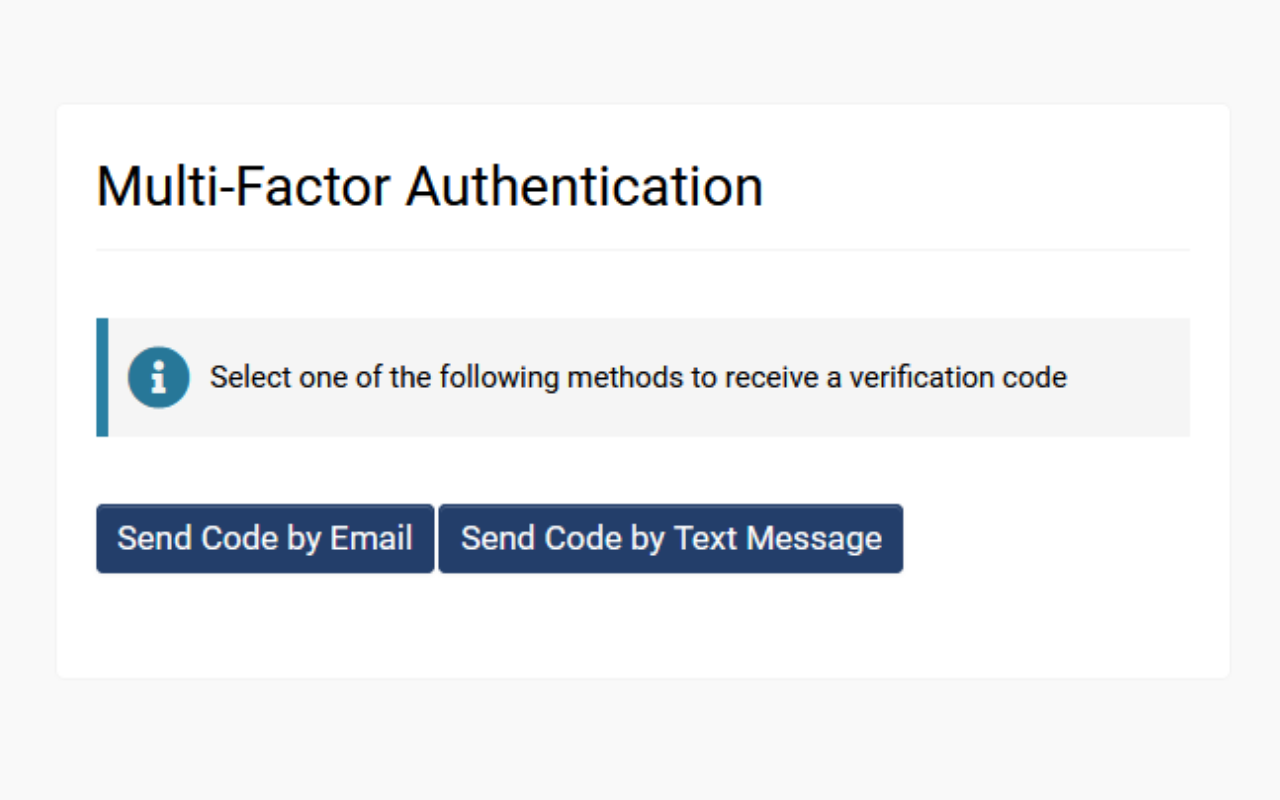
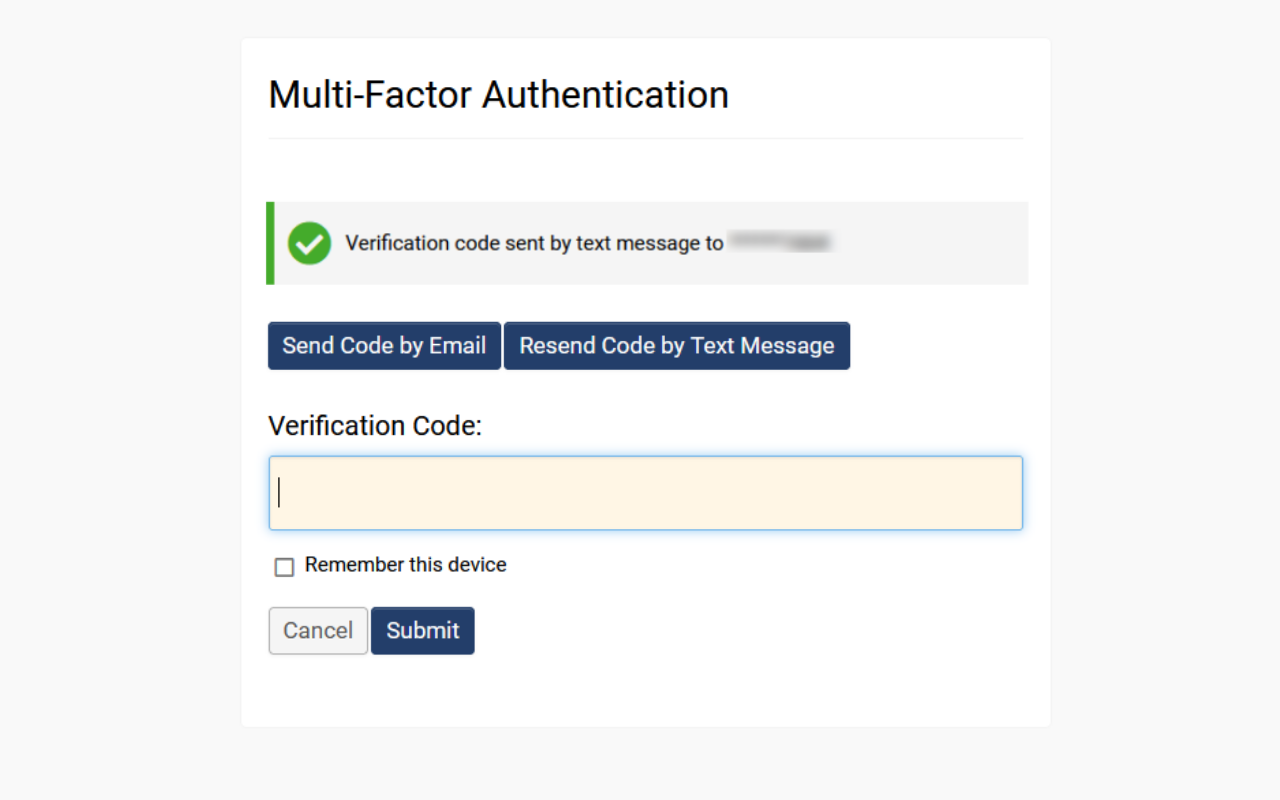
- When the user logs in, they will be presented with the option to receive a verification code via email (if available) or through SMS. The user can click Send Code by Text Message.
- The user can check their mobile messages, enter the code into the field, and then click Submit to finish authenticated login.
Configuration - Advanced
NOTE: When enabling MFA for use with TOTP all existing users in roles that will have 2-Factor enabled must first scan their code into an authenticator app.
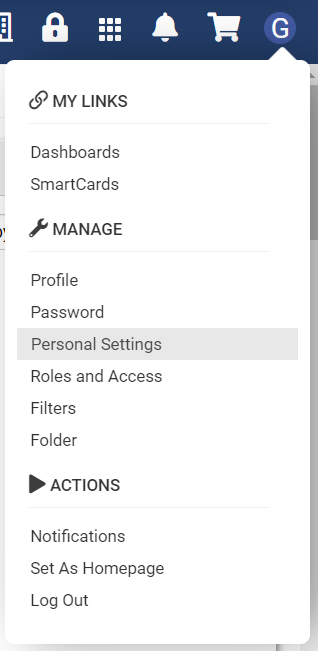
- Select the User menu from the top right.
- Select the link titled Personal Settings from the user menu.
- Select the Security tab in the following modal window.
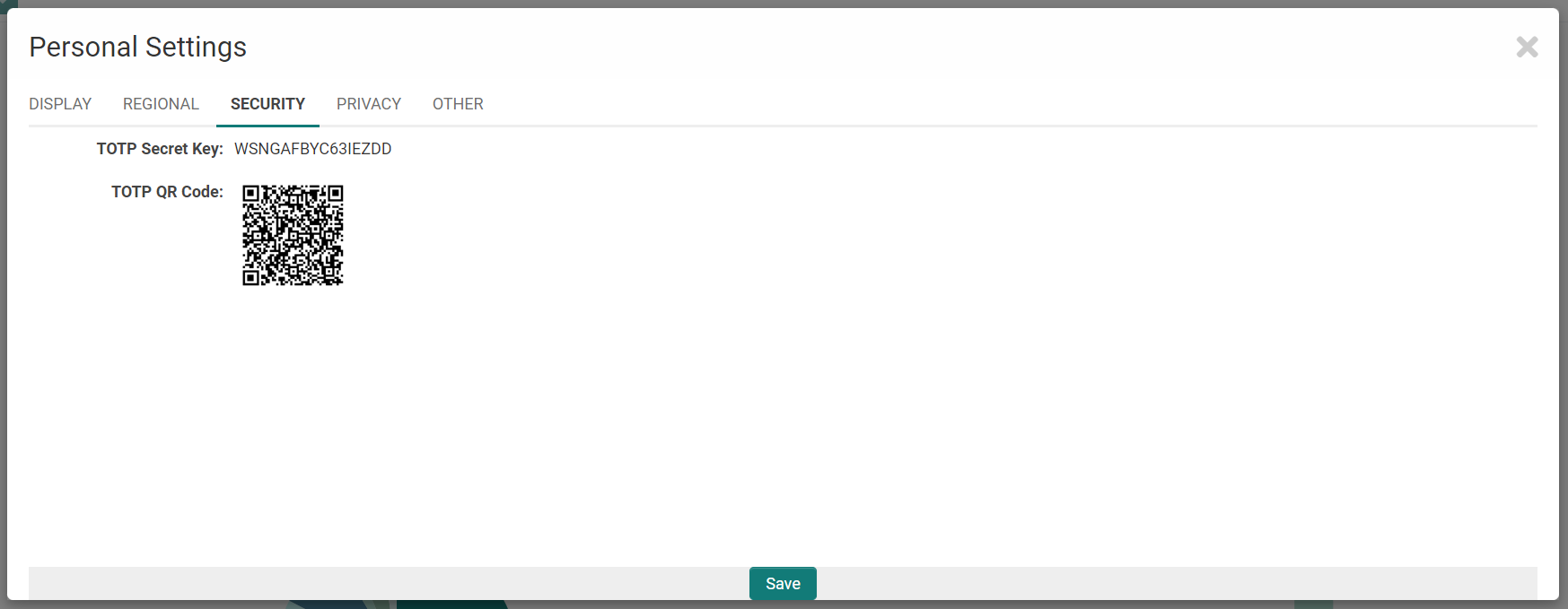
- Open your Authenticator app on your mobile device. If one is not yet installed on your device, download “Authenticator” from your mobile device’s app store.
- On your mobile device, in the Authenticator App, select “Add new device” or similar. Then “Scan QR Code” or similar.
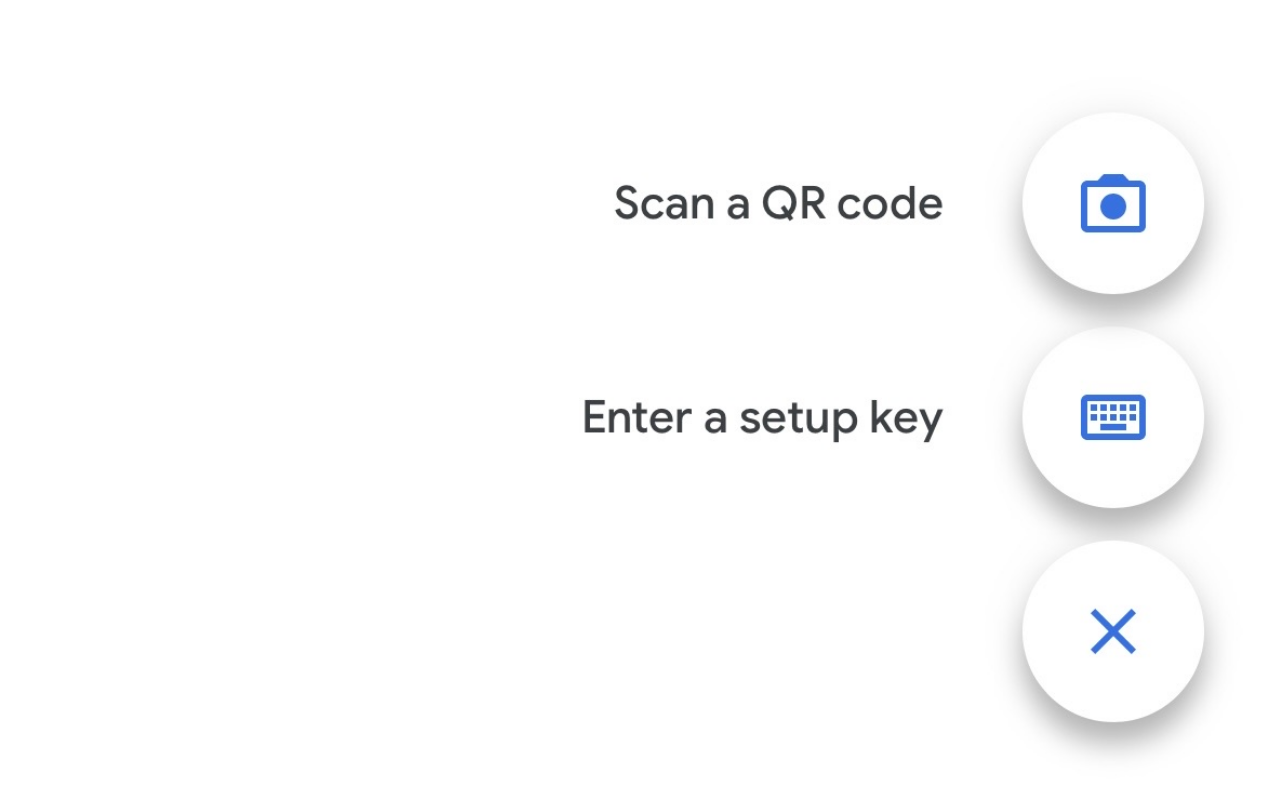
- Scan the QR code “TOTP QR Code” from within the app on your mobile device.
- A new device should be added to your list. Note that, alternatively, you can also use the “TOTP Secret Key” as opposed to the QR code.
- In your SmartSimple instance, in the Configuration Menu (9-Square Grid Icon), select Global Settings.
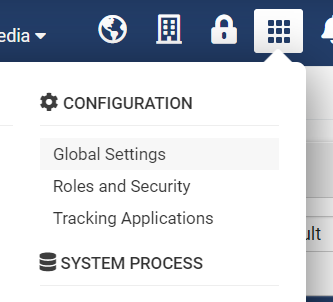
- Select the Security Tab from the Global Settings.
- Click Password and Activation Policies.
- Under “Authentication Options”, toggle on Enable Multi-Factor Authentication (MFA).
- In the setting Roles with Time-Based One-Time Password (TOTP) include the roles that you will be adding 2-Factor Authentication for. Note that the existing users in these roles must first scan the QR Code on their mobile device before this setting should be toggled on.
- Toggle on Enable Trusted Device if you would like users to be able to bypass entering a code for a time period after the code has been successfully entered. If enabled, also enter the time period that the 2-Factor Authentication will be bypassed for trusted users.
- Scroll to the bottom of the page and click Save.
- To test your MFA, log out of your account, and then log back in. You should now see a page following login called “Multi-Factor Authentication.” Enter the password in the Authenticator app here, and access will be granted into the system.
NOTE: To enable MFA for use with TOTP for existing users or before logging into system
- From the login screen select the "Forgot Password" link and enter the email used to login to your system
- In the email received select the activation link
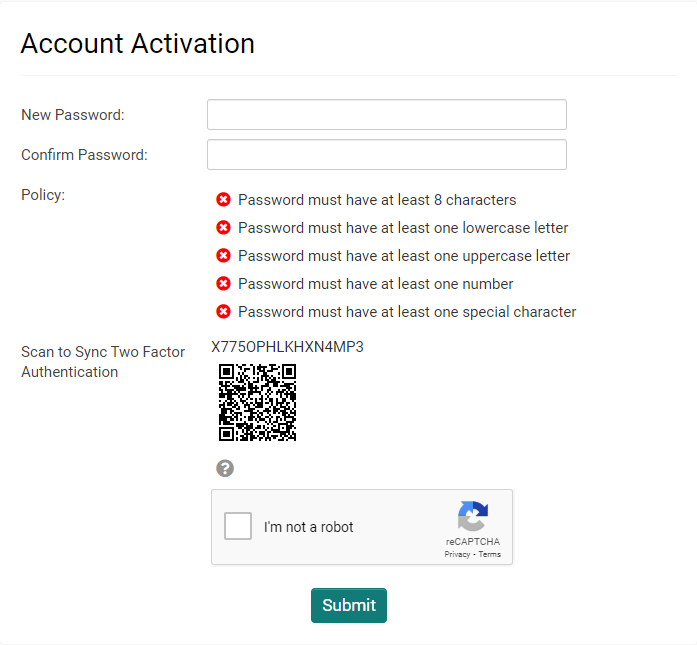
- You will be taken to the following screen:
- Enter in your new password and use the steps in the previous section above to link to your authenticator app using the QR code at this time before submitting.
Settings Explained
|
Setting |
Description |
|
Enable Multi-Factor Authentication |
Enables MFA for the entire instance but does not have any impact unless user roles are specified. |
|
Roles with Time-based One-time Password (TOTP) |
Associates one or more roles with authentication proven through an authenticator app such as Google or Microsoft Authenticator. |
|
Roles with Verification Code via SMS or Email |
Associates one or more roles with authentication proved through either email or an SMS message. The user can choose at the point of verification to receive an email containing the one-time-code or an SMS message containing the one-time code. SMS must be enabled by SmartSimple and will incur an additional cost. Please speak to your account manager for more information. |
|
Enable Trusted Device |
This option is used to enable the trusted device feature. If this option is selected then every user (via their role) associated with MFA will not be prompted every time they attempt to log into the system. |
|
Trusted Device Expiry |
Sets the frequency of the MFA prompt, based on the number of days specified. If the number is set to one, the user will be prompted every day for an MFA verification code, if set to five then the user will be prompted every five days. |